VPS Password Management Best Practices For Automated Trading Security
Protect your broker account and automated strategies with robust VPS security. Implement 16+ character passwords, 2FA, and RDP hardening to stay secure 24/7.


VPS password management for automated trading security combines strong unique credentials, two-factor authentication, and proper credential storage to protect trading servers running 24/7 strategies. Use a password manager for 16+ character passwords, enable 2FA on RDP and broker accounts, store API keys outside the VPS itself, and rotate credentials quarterly. Weak VPS security can expose broker credentials and active trading positions.
Key Takeaways
- Use a dedicated password manager (Bitwarden, 1Password, KeePass) with a 16+ character master password and unique credentials for every VPS, broker, and TradingView account.
- Enable two-factor authentication on RDP access, broker logins, and TradingView. Authenticator apps (Authy, Google Authenticator) beat SMS-based 2FA for trading accounts.
- Never store API keys, broker passwords, or webhook secrets in plain text files on the VPS itself. Use environment variables or encrypted credential vaults.
- Rotate VPS administrator passwords every 90 days and immediately after any suspected exposure or contractor access.
- Change the default RDP port (3389), restrict access by IP whitelist, and disable root/Administrator login over the network where possible.
Table of Contents
- Why VPS Password Security Matters For Automated Trading
- Credential Storage Best Practices
- Two-Factor Authentication Setup
- RDP And Remote Access Hardening
- Protecting Broker API Keys And Webhook Secrets
- Password Rotation And Incident Response
- Common Mistakes To Avoid
- Frequently Asked Questions
Why Does VPS Password Security Matter For Automated Trading?
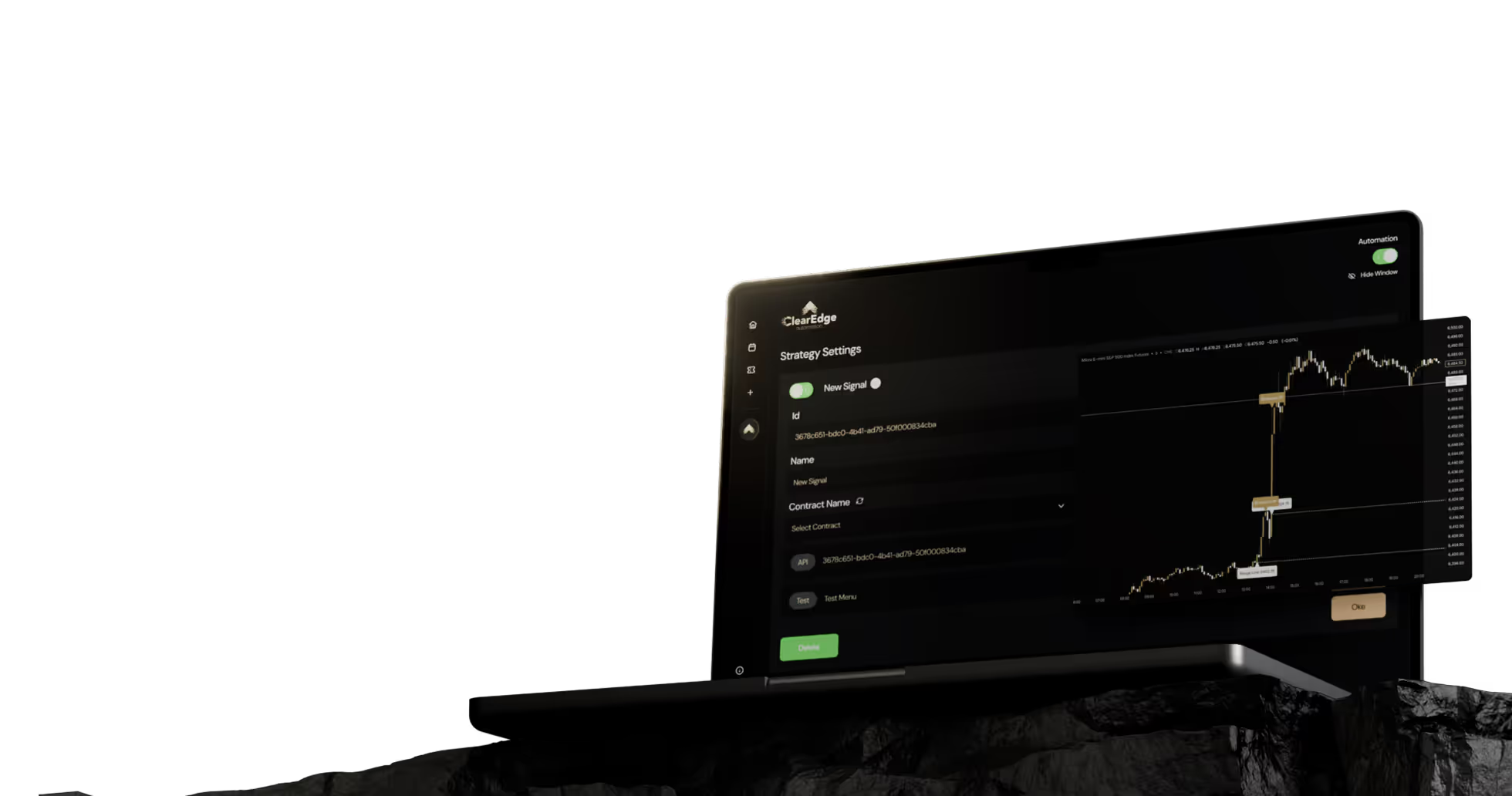
VPS password management for automated trading security matters because your trading server holds the keys to your broker account, your TradingView automation, and any open futures positions. A compromised VPS is not the same as a compromised email account. An attacker with admin access can place trades, drain margin, or alter your automation rules while you sleep.
Most retail traders run a virtual private server 24/7 to keep TradingView webhooks, broker connections, and trade copiers online. That always-on exposure is the trade-off for low latency and uptime. Strong password hygiene is what closes the gap. For broader context on VPS selection, see the VPS requirements for automated futures trading guide.
Trading VPS: A virtual private server, typically Windows or Linux, used to run trading platforms, webhook receivers, and automation scripts continuously. It matters because uptime and credentials directly affect whether your automated futures trading executes as designed.
Credential Storage Best Practices
Store every VPS, broker, and platform credential inside a dedicated password manager rather than browsers, sticky notes, or text files. A password manager generates unique 16-32 character passwords, encrypts them locally, and syncs across devices behind a single strong master password.
Password Manager: An encrypted vault application that stores and autofills credentials, generating unique random passwords for each account. For traders, it removes the temptation to reuse one password across the VPS, broker, and TradingView.
Recommended Storage Hierarchy
- Password manager vault: VPS admin password, broker login, TradingView account, RDP credentials.
- Hardware security key or authenticator app: Second factor for the password manager and broker.
- Encrypted offline backup: Recovery codes printed and stored in a fireproof safe, plus an encrypted USB copy.
- Never store on the VPS itself: Avoid plain text files, browser-saved passwords on the trading desktop, or unencrypted scripts containing credentials.
Master Password Requirements
Your password manager master password should be at least 16 characters, mix case and symbols, and be unique to that vault. Passphrases of 5-7 random words (Diceware style) are easier to remember and resist brute force attacks. Never reuse the master password anywhere else.
How Should You Set Up Two-Factor Authentication?
Enable two-factor authentication on every account that touches your trading stack: VPS provider login, RDP access where supported, broker account, TradingView, and your password manager. Use authenticator apps or hardware keys, not SMS, because SIM swap attacks have targeted retail traders.
Two-Factor Authentication (2FA): A login process requiring something you know (password) plus something you have (a code from an app or hardware key). For automated trading, 2FA blocks attackers even when passwords leak in unrelated breaches.
2FA Method Comparison
MethodSecurityBest ForHardware key (YubiKey)HighestBroker, password managerAuthenticator app (Authy, Google Authenticator)HighVPS provider, TradingView, RDP gatewaySMS text codesLowAvoid where possible (SIM swap risk)Email codesLow-MediumBackup only, not primary
2FA Setup Order
- Enable 2FA on your email account first. Email is the recovery path for everything else.
- Enable 2FA on the password manager.
- Enable 2FA on the VPS provider control panel (where you reboot, rebuild, or access console).
- Enable 2FA on the broker account and TradingView.
- Print and store recovery codes offline. Losing 2FA without backups can lock you out during market hours.
RDP And Remote Access Hardening
Remote Desktop Protocol is the most common attack surface on a Windows trading VPS because port 3389 is constantly scanned by automated bots. Reduce exposure by changing the default port, restricting access by IP, requiring 2FA on a gateway, and using Network Level Authentication.
RDP Hardening Checklist
- Change RDP from default port 3389 to a non-standard high port (above 49152).
- Restrict inbound RDP to your home or office IP via the VPS firewall.
- Enable Network Level Authentication (NLA) so credentials are checked before the session opens.
- Rename the default Administrator account and disable it after creating a new admin user.
- Set account lockout after 5 failed attempts for 15+ minutes to slow brute force attempts.
- Use a VPN or RDP gateway with 2FA rather than exposing RDP directly to the internet.
- For Linux VPS, disable password SSH login and use SSH keys with passphrases, plus fail2ban.
Network Level Authentication (NLA): A Windows RDP feature that authenticates the user before establishing a remote session. It blocks unauthenticated resource consumption and many automated brute force tools.
Linux Trading VPS Notes
If you run a Linux VPS for webhook receivers or custom bots, disable password authentication in /etc/ssh/sshd_config, use ed25519 SSH keys, and run fail2ban to auto-ban IPs after failed attempts. UFW or iptables should block all ports except SSH (on a non-default port) and your webhook listener.
How Do You Protect Broker API Keys And Webhook Secrets?
Treat broker API keys and TradingView webhook secrets like cash. Anyone with the API key can place orders, and anyone with the webhook URL plus secret can trigger trades. Store them as environment variables or in encrypted secret managers, never in plain text scripts checked into Git or sitting in your Documents folder.
API Key Protection Rules
- Generate read-only keys for monitoring scripts and trade-enabled keys only where execution is needed.
- Restrict API keys by IP address to your VPS public IP wherever the broker supports it.
- Set position size and order count limits on the broker side as a second line of defense.
- Store keys in environment variables or a secret manager (AWS Secrets Manager, HashiCorp Vault, or simple OS-level credential stores).
- Never commit credentials to GitHub, even in private repos. Use .gitignore and pre-commit scanning.
- Use a long random webhook secret token and validate it on every incoming TradingView alert. See TradingView webhook security best practices for details.
Webhook Secret: A random token included in TradingView alert payloads and verified by your automation receiver. It prevents attackers who guess your webhook URL from triggering unauthorized trades.
Password Rotation And Incident Response
Rotate VPS administrator passwords, broker passwords, and API keys every 90 days, and immediately after any contractor access, suspicious login alert, or known third-party breach involving your email. Rotation limits how long a leaked credential stays useful.
Rotation Schedule
CredentialRotation FrequencyTrigger EventsVPS admin password90 daysContractor access, breach alertBroker login90-180 daysLogin from unknown IPBroker API keys90 daysSuspicious order activityWebhook secrets180 daysWebhook URL exposureSSH keysAnnuallyLost laptop, team change
Incident Response Steps
- Disable the broker API key first. This stops any trade execution.
- Flatten open positions manually through the broker if you cannot trust automation.
- Change the VPS admin password and revoke active RDP sessions.
- Rotate the webhook secret and update TradingView alerts.
- Review broker order history and VPS auth logs for the past 30 days.
- Re-enable trading only after credentials and 2FA are verified clean.
Common Mistakes To Avoid
- Reusing passwords across the VPS, broker, and email. One breach cascades into all three.
- Saving broker passwords in browsers on the VPS. Anyone with RDP access can read them.
- Using SMS 2FA for broker accounts. SIM swap attacks have drained funded trading accounts.
- Leaving RDP open to 0.0.0.0 on port 3389. Bots will find it within hours.
- Skipping recovery code backups. A lost phone during NFP or FOMC can lock you out of your broker.
Frequently Asked Questions
1. Should I use the same password manager on my VPS and personal laptop?
Yes, use the same password manager account on both, secured with a strong master password and 2FA. Syncing the vault is safer than maintaining separate password lists, since it removes the temptation to reuse weak credentials on the trading server.
2. Is RDP safe for automated futures trading if I keep it patched?
RDP can be safe when hardened with a non-default port, IP whitelisting, NLA, account lockout policies, and 2FA via a VPN or gateway. Patching alone is not enough because brute force and credential stuffing attacks bypass unpatched and patched systems alike.
3. How long should my VPS administrator password be?
Use a minimum of 16 characters with mixed case, numbers, and symbols, generated by a password manager. Length matters more than complexity tricks, so a 20-character random string is stronger than an 8-character "P@ssw0rd!" pattern.
4. Can I store TradingView webhook URLs in plain text?
The webhook URL itself is not a secret if you include a strong secret token in the alert payload that your receiver validates. Treat the secret token like an API key, store it in an encrypted vault, and rotate it if you ever share screenshots or stream your setup.
5. What happens to my open positions if my VPS gets compromised?
An attacker with VPS access could potentially place trades through saved broker sessions or stored API keys, exposing your account to forced losses. Broker-side IP restrictions, API key permission limits, and 2FA on broker withdrawals reduce the damage if a VPS is breached.
6. Should I use Windows or Linux for a more secure trading VPS?
Linux generally has a smaller attack surface and stronger default SSH security, but Windows is required for most retail trading platforms like NinjaTrader and TradeStation. The platform you can secure correctly is more important than the operating system, so pick what matches your trading software and harden it.
Conclusion
Strong VPS password management is the foundation of automated trading security: unique long passwords in a manager, 2FA via authenticator app or hardware key, hardened RDP or SSH, protected broker API keys, and a 90-day rotation schedule. None of these steps cost much, and together they remove the most common attack paths against retail trading servers.
For deeper coverage of VPS selection, speed tiers, and integrated platform options, read our complete guide to VPS for automated futures trading. Pair good security habits with paper trading and forward testing before deploying any automated strategy live.
Want to dig deeper? Read our complete guide to VPS for automated futures trading for detailed setup instructions, speed tier comparisons, and cost optimization tips.
References
- National Institute of Standards and Technology. "Digital Identity Guidelines (SP 800-63B)." https://pages.nist.gov/800-63-3/sp800-63b.html
- Microsoft Learn. "Configure Network Level Authentication for RDP." Microsoft Documentation
- CISA. "Securing Remote Desktop (RDP) for Home and Business." CISA Guidance
- CFTC. "Customer Advisory: Beware of Cyber Threats." CFTC Customer Advisories
Disclaimer: This article is for educational purposes only. It is not trading advice. ClearEdge Trading executes trades based on your rules, it does not provide signals or recommendations.
Risk Warning: Futures trading involves substantial risk. You could lose more than your initial investment. Past performance does not guarantee future results. Only trade with capital you can afford to lose.
CFTC RULE 4.41: Hypothetical results have limitations and do not represent actual trading.
By: ClearEdge Trading Team | 29+ Years CME Floor Trading Experience | About
Steal the PlaybooksOther TradersDon’t Share
Every week, we break down real strategies from traders with 100+ years of combined experience, so you can skip the line and trade without emotion.