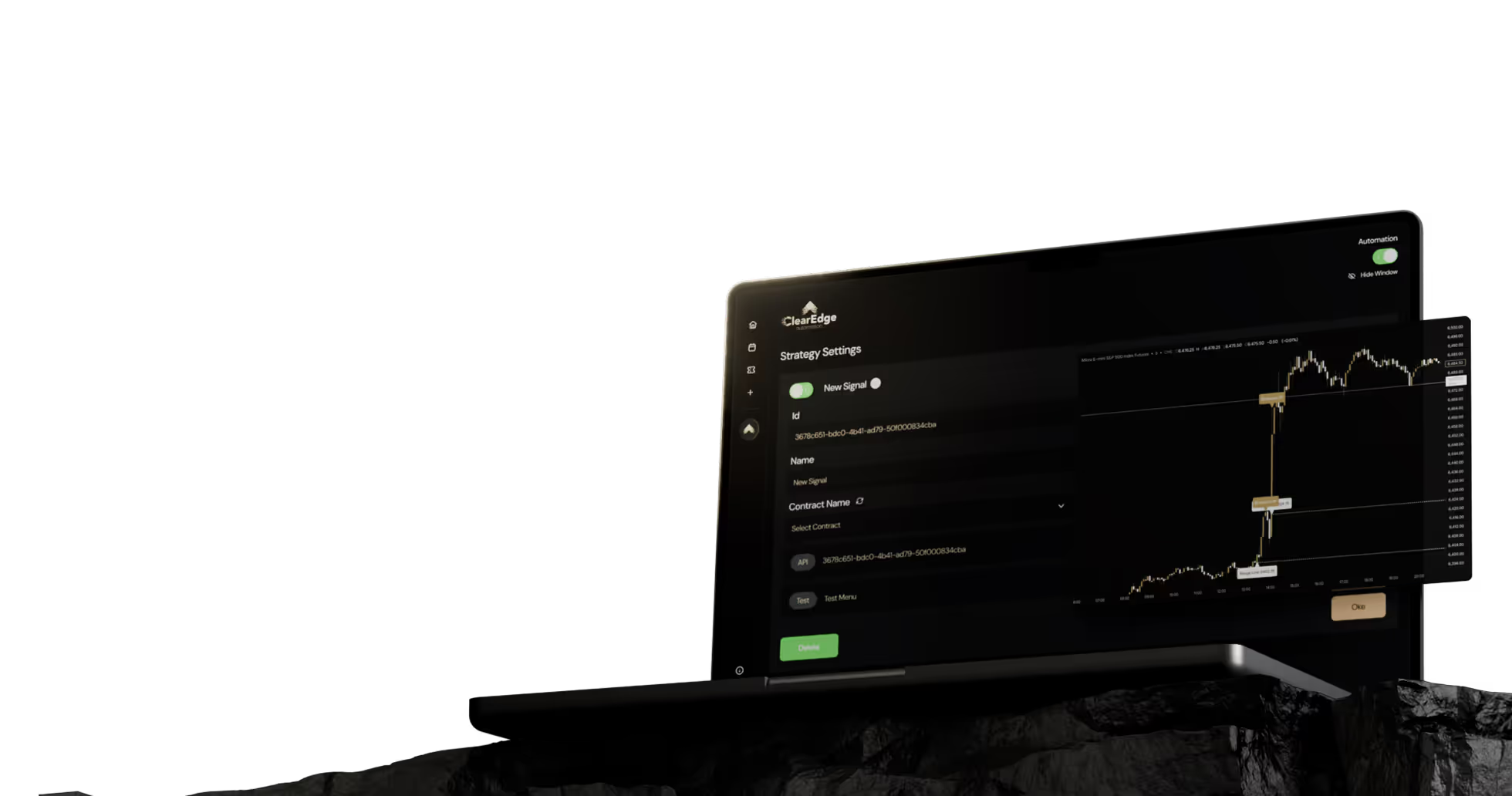
How To Secure TradingView Webhooks For Automated Futures Trading
Protect your automated trades from malicious alerts. Secure TradingView webhooks using token authentication, IP allowlisting, and encrypted credential storage.


TradingView webhook security for automated futures trading depends on three core controls: token authentication in your JSON payload, IP allowlisting to restrict incoming requests to TradingView's servers, and encrypted credential storage on your automation platform. Without these layers, a leaked webhook URL can let anyone send fake orders to your broker account.
Key Takeaways
- TradingView webhook URLs are public endpoints, anyone with the URL can send a POST request unless you add authentication.
- Token authentication embedded in the JSON payload is the minimum security baseline for live trading webhooks.
- IP allowlisting should restrict incoming alerts to TradingView's published IP ranges (52.89.214.238, 34.212.75.30, 54.218.53.128, 52.32.178.7).
- Broker API keys should never appear in webhook payloads, store them encrypted on the automation platform side.
- Rotate tokens after any suspected leak, after sharing scripts publicly, or every 90 days as standard hygiene.
Table of Contents
- Why Webhook Security Matters for Automated Trading
- Token Authentication in Webhook Payloads
- IP Allowlisting for TradingView Webhooks
- Credential Storage Best Practices
- Common Webhook Security Mistakes
- Frequently Asked Questions
Why Does TradingView Webhook Security Matter for Automated Trading?
TradingView webhook security for automated trading matters because the webhook URL on your automation platform is a public HTTPS endpoint. Anyone who obtains that URL, through a screen share, a leaked screenshot, a shared Pine Script, or browser history, can send POST requests that your platform will treat as legitimate alerts unless you've added authentication.
The risk is not theoretical. A leaked webhook combined with predictable JSON formatting lets an attacker submit fake orders, drain margin through repeated trades, or trigger stop-outs at the worst possible moment. For futures traders running ES, NQ, or CL contracts where one tick can be $10-$12.50, an unauthorized order on a leveraged account is a serious problem.
Webhook URL: A unique HTTPS endpoint that receives POST requests from TradingView when an alert fires. It is public by design, security comes from what's inside the request body, not the URL itself.
Three controls handle most of the risk: token authentication in the payload, IP allowlisting at the platform layer, and proper credential storage so broker API keys never travel through TradingView. The rest of this article walks through each.
How Does Token Authentication Protect Your Webhook?
Token authentication adds a secret string to your JSON payload that the automation platform validates before processing the alert. If the token is missing or wrong, the request is rejected before it ever touches your broker connection. This is the single most effective control for tradingview webhook security.
A typical authenticated alert message format looks like this:
{
"token": "a8f3k2-9xq7-bn4m-7vp2-rh8w4t6c1xz9",
"symbol": "ESZ2025",
"action": "buy",
"quantity": 1,
"order_type": "market"
}
The token should be long (32+ characters), random, and unique per alert template or per strategy. Treat it like a password. Don't reuse the same token across multiple Pine Script automation setups, and never paste a real token into a public Pine Script you plan to share.
Token Authentication: A shared secret embedded in the webhook payload that the receiving server checks before executing the trade. It is the minimum bar for a live trading webhook.
If you're setting up your first webhook, the TradingView webhook setup guide walks through the full configuration including where the token sits inside the JSON payload. For format-specific questions, the JSON payload format reference covers required and optional fields.
What Happens if a Token Leaks?
Rotate it. Generate a new token, update both your alert messages in TradingView and the platform configuration, then delete the old one. Common leak sources include shared TradingView strategies, Discord screen shares, support tickets that include alert message content, and screenshots posted to social media.
How Does IP Allowlisting Add a Second Layer of Defense?
IP allowlisting restricts the automation platform to only accept webhook requests from TradingView's known server IP addresses. Even if someone obtains your webhook URL and token, requests from any other IP get blocked at the network layer.
TradingView publishes the IP ranges its alert servers use. As of late 2025, the documented IPs are:
- 52.89.214.238
- 34.212.75.30
- 54.218.53.128
- 52.32.178.7
These can change, so check TradingView's official webhook documentation periodically. Most reputable automation platforms either implement allowlisting automatically or expose it as a configuration option. If your platform doesn't support IP filtering at all, that's worth flagging.
IP Allowlist: A list of approved source IP addresses permitted to send requests to your webhook endpoint. Requests from unlisted IPs are dropped before the application processes them.
Allowlisting is defense in depth, not a replacement for token authentication. Use both. Token auth catches anyone who happens to be sending from a TradingView IP (rare but possible in shared infrastructure), while IP filtering catches anyone trying to replay your token from a different source.
Where Should Broker Credentials Actually Live?
Broker API keys, account numbers, and login credentials should be stored encrypted on the automation platform side, never in the TradingView alert message. The webhook payload should only carry the trading instruction (symbol, action, quantity), not authentication for your broker.
This separation matters because TradingView alert messages are visible in several places: the alert configuration UI, browser local storage, sometimes server logs, and any backup of your TradingView account. If your broker credentials sit in the alert body, every one of those locations becomes a credential exposure point.
A properly designed automation platform stores broker credentials in encrypted-at-rest storage, decrypts them only at execution time inside an isolated process, and never logs them in plaintext. When you connect a broker through supported broker integrations, the credentials should be entered once on the platform and referenced by an internal account ID in your alerts, not transmitted with each webhook.
Credential Storage: The way an automation platform holds broker API keys and login data. Encrypted-at-rest storage with isolated decryption is the baseline standard.
What Should the Webhook Payload Reference Instead?
An account alias or internal ID. For example, send "account": "main-prop-account" rather than embedding the actual broker login. The platform looks up the credential server-side using that alias. If the webhook payload leaks, the attacker learns your account label, not how to log into your broker.
Common Webhook Security Mistakes to Avoid
A few patterns show up repeatedly in support tickets and post-incident reviews. Avoiding them handles most of the practical risk.
- Reusing tokens across strategies. If one Pine Script gets shared publicly, every webhook using that token is compromised. Generate unique tokens per alert template.
- Putting broker credentials in the alert message. The alert body is not a secure channel. Reference accounts by alias and store credentials on the platform.
- Skipping IP allowlist setup. Most platforms support it, many traders never enable it. Turn it on.
- Never rotating tokens. Treat token rotation like password rotation. Every 90 days minimum, immediately after any suspected leak.
- Sharing screenshots with the webhook URL visible. Crop or redact before posting in Discord, forums, or support tickets.
For broader troubleshooting beyond security, the webhook troubleshooting guide covers delivery and connection failures, and the webhook security best practices article goes deeper on operational hygiene.
Plan Tier Considerations
Webhook functionality requires TradingView Essential plan or higher. Alert frequency limits vary by plan tier, and faster alert delivery speed on higher tiers reduces the window where stale alerts could be replayed if intercepted. None of this replaces token authentication, but plan tier affects how quickly your custom alert template reaches the platform.
Want the complete picture on alerts, webhooks, and execution? Read our TradingView automation guide for futures traders for end-to-end setup including security, formatting, and broker integration.
Frequently Asked Questions
1. Is the TradingView webhook URL itself a secret?
It should be treated as one, but assume it will leak eventually. Real security comes from token authentication and IP allowlisting, not from keeping the URL private.
2. How often should I rotate my webhook tokens?
Every 90 days as standard hygiene, and immediately after any suspected exposure such as sharing a Pine Script, screen sharing, or posting screenshots. Rotation takes a few minutes and eliminates risk from past leaks.
3. Can someone reverse-engineer my JSON payload to send fake orders?
Yes, if they have the webhook URL and there's no token authentication. JSON payload structure is predictable, so format alone is not security. Token validation is what stops unauthorized requests.
4. Does HTTPS alone make my webhook secure?
HTTPS encrypts the request in transit, which prevents network eavesdropping, but it does not authenticate the sender. Anyone with the URL can still send a valid HTTPS POST. You need token authentication on top of HTTPS.
5. Should I store my broker API key in the TradingView alert message?
No. Broker credentials should live encrypted on the automation platform. The alert message should only carry the trading instruction and a token, never broker login data.
6. What if my automation platform doesn't support IP allowlisting?
Token authentication still provides meaningful protection, but the lack of IP filtering is a reduced security posture. For live futures accounts with real capital, prefer platforms that implement both controls.
Conclusion
TradingView webhook security for automated trading comes down to three layered controls: token authentication inside every JSON payload, IP allowlisting restricted to TradingView's published server ranges, and encrypted credential storage so broker keys never travel through alert messages. Skip any one and the other two have to work harder.
Set up token rotation on a calendar, verify your platform supports IP filtering, and audit your existing alerts for any embedded broker credentials. Paper trade first to validate your strategy and security configuration before connecting a live funded account.
References
- TradingView - About Webhooks Documentation
- U.S. Commodity Futures Trading Commission
- CME Group - Futures Contract Specifications
- TradingView - Pine Script Alerts Reference
Disclaimer: This article is for educational purposes only. It is not trading advice. ClearEdge Trading executes trades based on your rules, it does not provide signals or recommendations.
Risk Warning: Futures trading involves substantial risk. You could lose more than your initial investment. Past performance does not guarantee future results. Only trade with capital you can afford to lose.
CFTC RULE 4.41: Hypothetical results have limitations and do not represent actual trading.
By: ClearEdge Trading Team | About
Steal the PlaybooksOther TradersDon’t Share
Every week, we break down real strategies from traders with 100+ years of combined experience, so you can skip the line and trade without emotion.