TradingView Webhook Security Best Practices For Automated Trading Protection
Shield your automated trading strategy from breaches using encryption, authentication tokens, and IP whitelisting to secure your TradingView webhook connection.


TradingView webhook URL security best practices protect your automated trading system from unauthorized access, data breaches, and fraudulent order execution. Essential measures include using HTTPS encryption, implementing authentication tokens, restricting IP addresses, rotating webhook URLs periodically, validating JSON payloads, and monitoring webhook logs for suspicious activity. These practices prevent attackers from intercepting your alert data or sending fake signals to your broker.
Key Takeaways
- Always use HTTPS for webhook URLs to encrypt data in transit between TradingView and your automation platform
- Implement authentication tokens or secret keys to verify that incoming webhook requests are legitimate
- Restrict webhook access by IP address whitelist to block unauthorized sources
- Rotate webhook URLs every 30-90 days to minimize exposure from potential leaks
- Monitor webhook logs daily to detect unusual activity patterns or failed authentication attempts
Table of Contents
- What Are Webhook Vulnerabilities in TradingView Automation?
- Why HTTPS Encryption Is Non-Negotiable
- How to Implement Webhook Authentication
- Using IP Address Restrictions
- Webhook URL Rotation Strategy
- Validating JSON Payloads
- Security Monitoring and Alert Logging
- Frequently Asked Questions
- Conclusion
What Are Webhook Vulnerabilities in TradingView Automation?
Webhook vulnerabilities occur when attackers intercept, modify, or forge the automated messages between TradingView and your broker execution platform. Because TradingView automation relies on webhooks to transmit alert data containing trade instructions, any security weakness in this communication channel can result in unauthorized trades, account access, or strategy theft.
Webhook: A webhook is an HTTP callback that sends real-time data from one application to another when a specific event occurs. In TradingView automation, webhooks transmit alert conditions and trade parameters to your execution platform.
Common attack vectors include man-in-the-middle interception of unencrypted traffic, replay attacks using captured webhook data, and brute-force discovery of publicly accessible webhook URLs. The 2024 OWASP API Security Top 10 identifies broken authentication and excessive data exposure as leading vulnerabilities affecting webhook implementations.
For futures traders using automated execution, webhook compromise can trigger unauthorized positions during volatile market conditions. An attacker who captures your webhook URL and JSON payload structure could send fake alerts to open positions, modify stop losses, or flatten profitable trades.
Why HTTPS Encryption Is Non-Negotiable
HTTPS encryption using TLS 1.2 or higher protects webhook data in transit by encrypting the connection between TradingView's servers and your automation platform. Without HTTPS, your webhook URL, authentication tokens, and trade parameters travel across the internet in plain text, visible to anyone monitoring network traffic.
TradingView supports HTTPS webhook URLs by default, but your receiving endpoint must have a valid SSL/TLS certificate. Self-signed certificates will cause webhook delivery failures. Use certificates from recognized certificate authorities like Let's Encrypt, which provides free automated SSL certificates.
According to Mozilla's TLS configuration guidelines, disable TLS 1.0 and 1.1 on your webhook endpoints. Configure your server to support only TLS 1.2 and 1.3 with strong cipher suites like AES-256-GCM. Weak ciphers like RC4 or 3DES create vulnerabilities even when HTTPS is enabled.
ProtocolSecurity LevelRecommendationHTTPNone - Plain textNever useHTTPS with TLS 1.0/1.1Weak - Known vulnerabilitiesDisableHTTPS with TLS 1.2StrongMinimum acceptableHTTPS with TLS 1.3Very StrongPreferred
How to Implement Webhook Authentication
Authentication tokens verify that incoming webhook requests originate from TradingView rather than an attacker. Include a secret token in your webhook URL query string or JSON payload that your automation platform validates before processing any trade instructions.
Generate authentication tokens using cryptographically secure random strings of at least 32 characters. Avoid predictable values like account numbers, email addresses, or simple passwords. Tools like OpenSSL can generate secure tokens: openssl rand -hex 32 produces a 64-character hexadecimal string.
Authentication Token: A secret string embedded in your webhook that proves the request came from an authorized source. Your automation platform checks this token before executing any trades from the webhook.
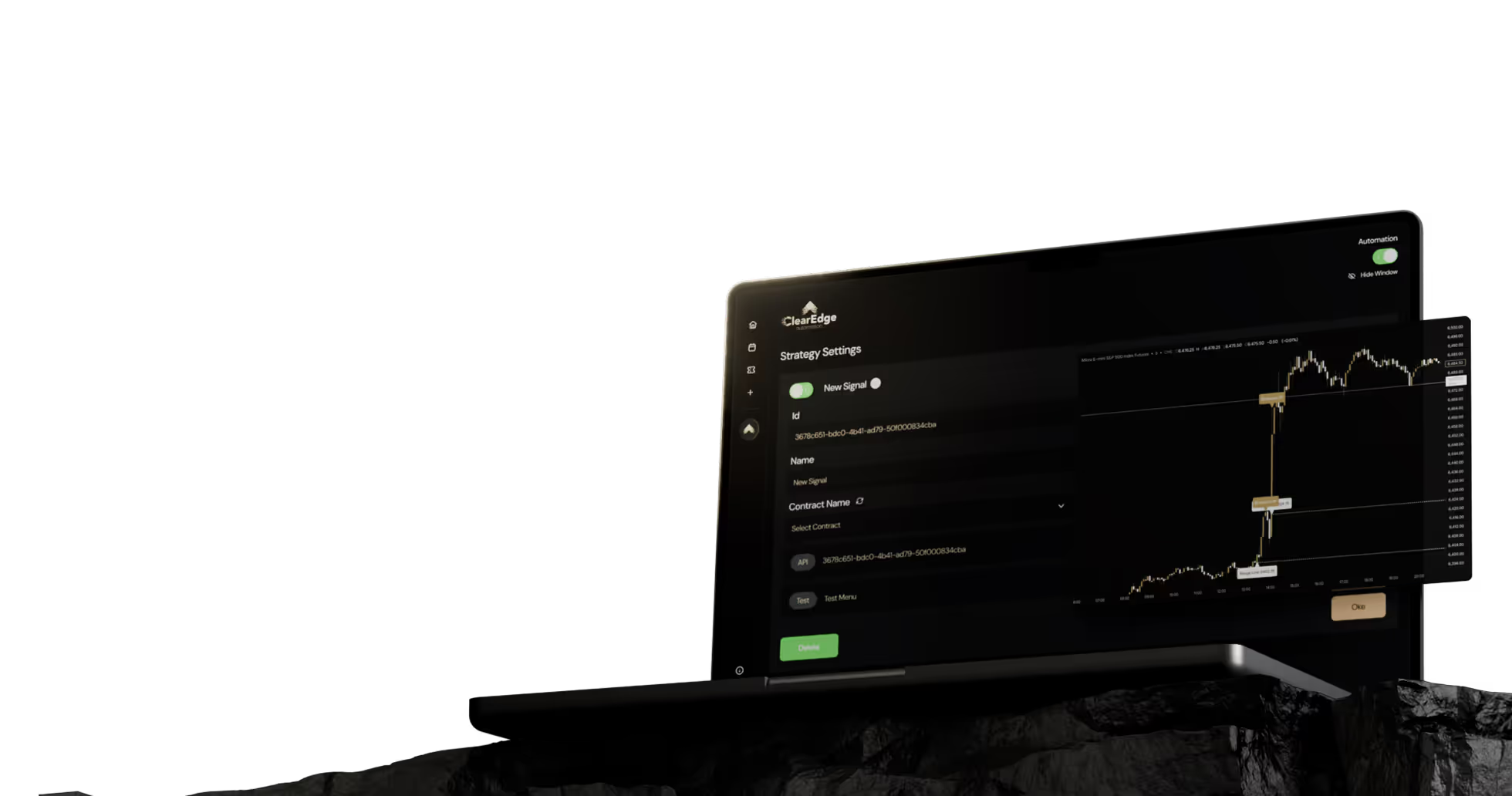
Store tokens securely in environment variables or encrypted configuration files, never in publicly accessible code repositories. Platforms like ClearEdge Trading include built-in token validation to verify webhook authenticity before sending orders to your broker.
For added security, implement HMAC (Hash-based Message Authentication Code) signatures. TradingView doesn't natively support HMAC for webhooks, but you can structure your JSON payload to include a signature field calculated from your alert parameters and secret key. Your receiving endpoint recalculates the signature and compares it to verify integrity.
Using IP Address Restrictions
IP address whitelisting limits webhook access to known TradingView server addresses, blocking requests from unauthorized sources. Configure your firewall or application-level access controls to accept webhook connections only from TradingView's published IP ranges.
TradingView's webhook requests originate from their cloud infrastructure. While TradingView doesn't publish a static IP list due to their distributed architecture, you can implement rate limiting and geographic restrictions to reduce exposure. Most automation platforms run behind cloud load balancers that support IP filtering rules.
For self-hosted automation systems, configure your firewall to log and block repeated connection attempts from suspicious IP addresses. Tools like fail2ban automatically ban IPs after a threshold of failed authentication attempts, typically 3-5 failures within 10 minutes.
Advantages of IP Whitelisting
- Blocks brute-force attacks from discovering webhook URLs
- Reduces server load from invalid requests
- Provides audit trail of connection sources
Limitations
- Cloud platforms use dynamic IP ranges that change
- Legitimate requests may be blocked after infrastructure changes
- IP spoofing can bypass simple filters
Webhook URL Rotation Strategy
Regular webhook URL rotation limits the time window for compromised URLs to be exploited. If an attacker captures your webhook URL, rotating it every 30-90 days invalidates their access before they can cause significant damage.
Implement a rotation schedule aligned with your security posture. Conservative approaches rotate URLs monthly, while less sensitive implementations may rotate quarterly. Document your rotation dates and update all TradingView alerts that reference the old URL.
Webhook URL Rotation Checklist
- ☐ Generate new authentication token using secure random method
- ☐ Create new webhook endpoint with updated token
- ☐ Test new webhook with paper trading account first
- ☐ Update all active TradingView alerts with new URL
- ☐ Monitor both old and new URLs for 24-48 hours
- ☐ Disable old webhook endpoint after transition period
- ☐ Document rotation date and next scheduled rotation
Automate rotation where possible. Some automated futures trading platforms support dynamic webhook URLs that change automatically without requiring manual alert updates. This approach reduces human error during rotation.
Validating JSON Payloads
JSON payload validation ensures that incoming webhook data contains expected fields, data types, and value ranges before processing trade instructions. This prevents malformed or malicious payloads from causing execution errors or unintended positions.
Define a strict schema for your TradingView alert JSON payload. Reject any webhook that includes unexpected fields, missing required parameters, or values outside acceptable ranges. For example, a position size field should be validated as a positive number within your maximum position limits.
JSON Payload: The structured data sent in your TradingView webhook containing trade parameters like action (buy/sell), quantity, symbol, and order type. Validating this structure prevents processing of corrupted or malicious data.
Common validation rules include checking that action fields contain only "buy," "sell," "flatten," or other predefined commands, verifying that ticker symbols match your approved trading list, and confirming that price fields are realistic relative to current market values. A crude oil order at $1 per barrel or $10,000 per barrel should be rejected as invalid.
Implement input sanitization to prevent injection attacks. Treat all webhook data as untrusted input. Use parameterized queries or ORM frameworks when storing webhook data in databases to prevent SQL injection. Validate numeric fields as actual numbers before using them in calculations.
Security Monitoring and Alert Logging
Comprehensive webhook logging creates an audit trail for security analysis and debugging. Log every incoming webhook request with timestamp, source IP, authentication status, payload content, and execution result.
Monitor logs for suspicious patterns including repeated failed authentication attempts, webhooks received outside normal trading hours, unusually large position sizes, or multiple webhooks received in rapid succession. Set up alerts for anomalies that require immediate investigation.
According to NIST Cybersecurity Framework guidelines, retain webhook logs for at least 90 days to support incident response and forensic analysis. Store logs in a secure location separate from your trading system to prevent attackers from deleting evidence of compromise.
Log EventData to CaptureAlert ThresholdAuthentication FailureIP address, timestamp, attempted token3 failures in 10 minutesInvalid JSONRaw payload, validation errors5 malformed requests in 1 hourAfter-Hours ActivityTimestamp, alert trigger timeAny webhook outside configured hoursUnusual Position SizeRequested quantity vs. normal rangeExceeds 2x typical position size
Review logs weekly during normal operations and daily during periods of elevated security concern. Automated log analysis tools can identify patterns that manual review might miss. For traders using multiple broker connections, correlate webhook logs with broker execution confirmations to detect discrepancies.
Frequently Asked Questions
1. Should I include my authentication token in the URL or the JSON payload?
Including tokens in the JSON payload is more secure than URL query parameters because URLs often appear in server logs, browser history, and analytics tools. However, TradingView's webhook URL field limits your ability to dynamically change payload content, so URL-based tokens are more practical for most implementations.
2. How do I know if my webhook has been compromised?
Signs of compromise include unexpected trades appearing in your account, webhook logs showing requests from unfamiliar IP addresses, authentication failures from valid-looking requests with wrong tokens, or alerts triggering when your TradingView strategy shows no signals. Review your broker statements daily for unauthorized activity.
3. Can someone discover my webhook URL by monitoring TradingView's website?
No, webhook URLs are transmitted securely between TradingView's servers and the configured endpoint. The URL doesn't appear in client-side code or network traffic visible to other TradingView users. Compromise typically occurs through leaked configuration files, insecure sharing, or endpoint vulnerabilities.
4. What's the difference between TradingView webhook security and broker API security?
Webhook security protects the communication between TradingView and your automation platform, while broker API security protects connections between your platform and the futures broker. Both require separate security measures—webhook authentication tokens for TradingView and API keys for your broker integration.
5. Should I use a VPN for my automation server?
A VPN protects your automation server's outbound connections to brokers but doesn't secure inbound webhook traffic from TradingView. Focus on webhook-specific security measures like HTTPS, authentication tokens, and monitoring rather than relying on VPNs alone for security.
Conclusion
TradingView webhook URL security requires layered defenses including HTTPS encryption, authentication tokens, IP restrictions, regular URL rotation, payload validation, and comprehensive monitoring. No single measure provides complete protection—security comes from implementing multiple overlapping controls. Traders should audit their webhook security monthly and update practices as new vulnerabilities emerge in automated trading systems.
Want to learn more about TradingView automation? Read our complete guide to TradingView automation for setup instructions, strategy examples, and advanced configuration options.
References
- CISA - Understanding Man-in-the-Middle Attacks
- OWASP API Security Project - Top 10 Vulnerabilities
- Mozilla - TLS Configuration Guidelines
- NIST Special Publication 800-92 - Guide to Computer Security Log Management
Disclaimer: This article is for educational and informational purposes only. It does not constitute trading advice, investment advice, or any recommendation to buy or sell futures contracts. ClearEdge Trading is a software platform that executes trades based on your predefined rules—it does not provide trading signals, strategies, or personalized recommendations.
Risk Warning: Futures trading involves substantial risk of loss and is not suitable for all investors. You could lose more than your initial investment. Past performance of any trading system, methodology, or strategy is not indicative of future results. Before trading futures, you should carefully consider your financial situation and risk tolerance. Only trade with capital you can afford to lose.
CFTC RULE 4.41: HYPOTHETICAL OR SIMULATED PERFORMANCE RESULTS HAVE CERTAIN LIMITATIONS. UNLIKE AN ACTUAL PERFORMANCE RECORD, SIMULATED RESULTS DO NOT REPRESENT ACTUAL TRADING. ALSO, SINCE THE TRADES HAVE NOT BEEN EXECUTED, THE RESULTS MAY HAVE UNDER-OR-OVER COMPENSATED FOR THE IMPACT, IF ANY, OF CERTAIN MARKET FACTORS, SUCH AS LACK OF LIQUIDITY.
By: ClearEdge Trading Team | About
Steal the PlaybooksOther TradersDon’t Share
Every week, we break down real strategies from traders with 100+ years of combined experience, so you can skip the line and trade without emotion.