Automation Platform Data Privacy: Protect Your Trading Data
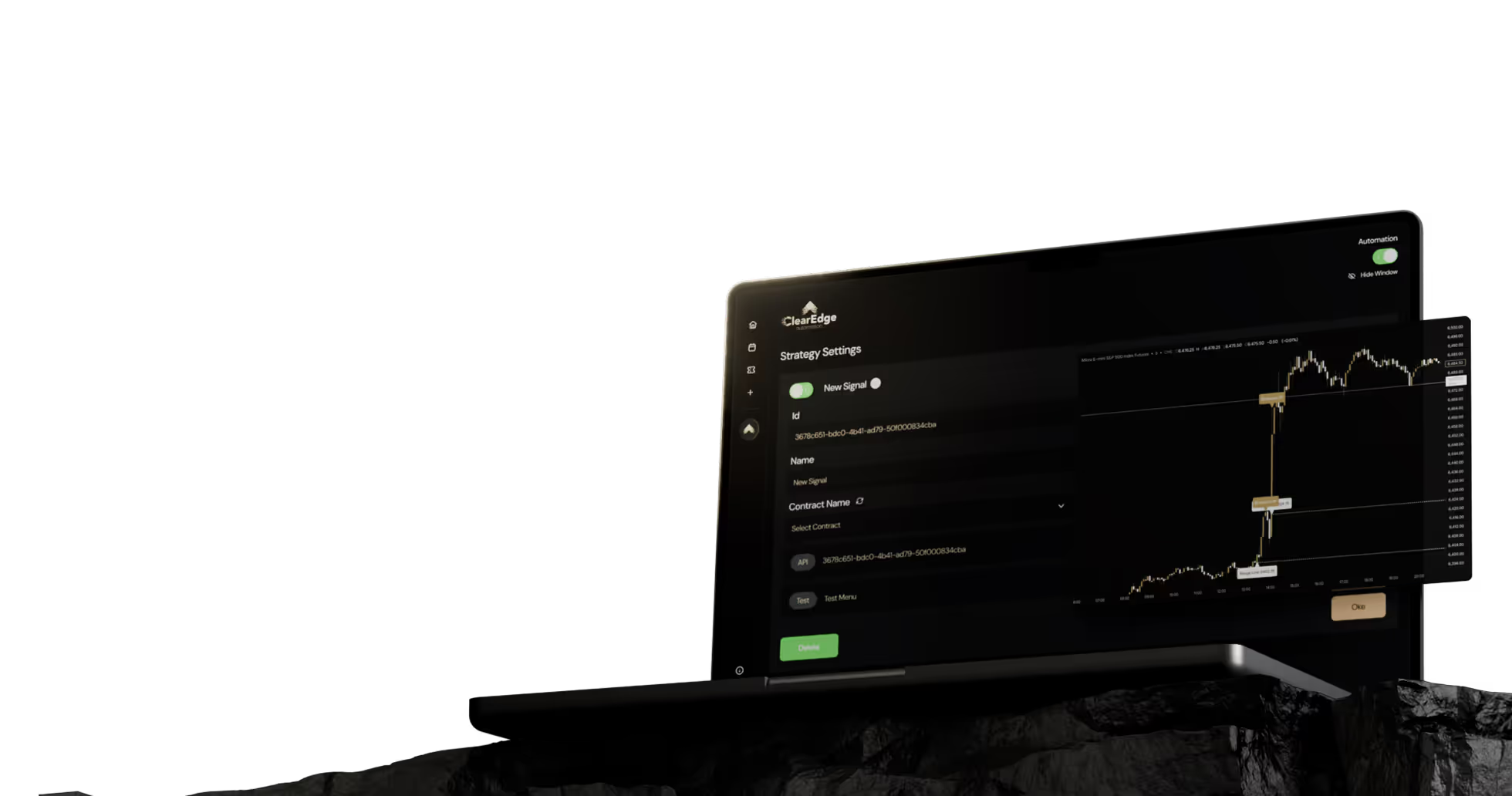
Secure your trading secrets and API keys. Evaluate automation platform privacy by auditing encryption standards, storage architecture, and SOC 2 compliance.


Automation platform data privacy considerations include how your trading data, strategies, API keys, and personal information are stored, encrypted, and shared. Key factors are encryption standards (TLS 1.3+, AES-256), data retention policies, third-party sharing practices, and compliance with regulations like GDPR and SOC 2. Platforms that store data locally or use end-to-end encryption offer stronger privacy than those storing unencrypted credentials on external servers.
Key Takeaways
- API keys and broker credentials should use encrypted storage with zero-knowledge architecture where the platform cannot access your keys
- Check whether platforms store your trading strategies server-side or client-side—local storage reduces exposure risk
- SOC 2 Type II certification and GDPR compliance indicate audited security practices and data handling standards
- Review data retention policies to understand how long platforms keep your trade history and personal information after account closure
Table of Contents
- What Data Do Automation Platforms Collect?
- How Should Platforms Encrypt Your Data?
- Where Is Your Data Stored?
- What About Third-Party Data Sharing?
- What Certifications Matter for Data Privacy?
- Frequently Asked Questions
- Conclusion
What Data Do Automation Platforms Collect?
Futures automation platforms typically collect three categories of data: authentication credentials (API keys, broker logins), trading strategy data (TradingView alerts, rules, parameters), and account activity (trade history, performance metrics, timestamps). The scope of collection varies—some platforms store full strategy logic server-side while others only process webhook payloads temporarily. Understanding what data flows through the platform helps you assess privacy risk before connecting live accounts.
API Key: An authentication token that grants an application access to your broker account for placing trades. API keys typically have permission levels—read-only, trade execution, or full account access.
Most platforms require read and trade execution permissions to function. Some also collect email addresses, payment information, IP addresses, and device identifiers for account management. For traders using prop firm accounts, additional scrutiny applies since funded accounts have specific data handling requirements in firm agreements.
The key question: does the platform store your credentials permanently or only use them in-session? Platforms that cache API keys indefinitely create a larger attack surface than those using token-based authentication with short expiration windows.
How Should Platforms Encrypt Your Data?
Strong encryption uses TLS 1.3 for data in transit and AES-256 for data at rest. TLS 1.3 protects data moving between your browser, the platform, and your broker by encrypting the connection. AES-256 encrypts stored data—if the platform's database were breached, encrypted credentials would be unreadable without decryption keys.
Look for platforms that implement encryption at multiple layers. Data transmitted from TradingView webhooks should use HTTPS endpoints. API keys stored in databases should be encrypted, not plaintext. Session tokens should expire and regenerate regularly. Some platforms add an extra layer called zero-knowledge encryption, where even the platform provider cannot decrypt your stored credentials—only you hold the decryption key.
Encryption TypeWhat It ProtectsImplementationTLS 1.3Data in transitHTTPS connections, webhook endpointsAES-256Data at restDatabase storage, credential vaultsZero-knowledgeStored credentialsClient-side encryption before uploadHashed passwordsAccount accessbcrypt, Argon2 for login passwords
Avoid platforms that transmit API keys via unencrypted email or allow credentials to be displayed in plaintext within the user interface. When evaluating platform options, ask specifically about encryption implementation—general claims of "bank-level security" are less meaningful than technical specifications.
Where Is Your Data Stored?
Automation platforms use server-side storage, client-side storage, or hybrid models. Server-side storage keeps your strategy rules, API keys, and settings on the platform's servers—convenient for accessing from multiple devices but creates centralized risk. Client-side storage keeps sensitive data on your local machine, syncing only execution commands to servers. Hybrid models store non-sensitive settings server-side while keeping credentials local.
Server-Side Storage: Data stored on the platform provider's servers, accessible from any device but dependent on the provider's security practices and vulnerable if servers are compromised.
Geographic location of servers matters for regulatory compliance. EU-based traders should verify GDPR compliance and whether data is stored within EU borders. U.S. traders may prefer platforms using U.S.-based data centers subject to domestic privacy laws. Some platforms use cloud providers like AWS or Google Cloud—check whether data is encrypted within these environments and whether the platform provider or cloud vendor controls encryption keys.
Data retention policies determine how long platforms keep your information after account closure. Some delete all data within 30 days of termination. Others retain trade history indefinitely for compliance or analytics. Review terms of service for specifics. For TradingView automation setups, consider whether your alert messages contain sensitive strategy details that get logged server-side.
What About Third-Party Data Sharing?
Most platforms share limited data with third parties—brokers receive order details, payment processors see billing information, and analytics tools may track user behavior. The privacy risk depends on what's shared and with whom. Responsible platforms disclose all third-party integrations in privacy policies and allow users to opt out of non-essential data sharing.
Broker integrations necessarily share trade instructions—symbol, quantity, order type, price. This data goes directly to your broker via API and doesn't typically pass through additional intermediaries. However, some platforms use middleware services for order routing or market data, adding another data touchpoint. Payment processors like Stripe or PayPal receive billing details but shouldn't access your trading data.
Minimal Data Sharing
- Direct broker API connections without intermediaries
- Payment processing isolated from trading data
- No sale of user data to third-party marketers
- Anonymous usage analytics only
Privacy Red Flags
- Sharing strategy details with "partners" for optimization
- Selling aggregated trade data to market researchers
- Using third-party analytics that track individual behavior
- Vague language about data usage in privacy policies
Read privacy policies for clauses about aggregated or anonymized data. Even if your name isn't attached, detailed trading patterns combined with account size and timestamps can sometimes be de-anonymized. Platforms serious about privacy explicitly state they don't monetize user data. For context on broader platform considerations, see our guide on broker integrations.
What Certifications Matter for Data Privacy?
SOC 2 Type II certification indicates a platform has undergone third-party audit of its security controls, including data handling, access management, and incident response. Type II audits evaluate controls over a 6-12 month period, providing more assurance than Type I (point-in-time) audits. GDPR compliance is required for platforms serving EU customers and demonstrates structured data protection practices even for non-EU users.
SOC 2 Type II: A security audit standard that evaluates a service provider's controls for Security, Availability, Processing Integrity, Confidentiality, and Privacy over an extended period, typically 6-12 months.
ISO 27001 certification covers information security management systems. PCI DSS compliance applies to platforms handling credit card data directly. These certifications require ongoing audits and remediation of identified gaps. They're not guarantees—certified companies still experience breaches—but they indicate investment in security infrastructure and accountability.
Check certification dates and renewal status. A SOC 2 report from three years ago without renewal suggests lapsed security practices. Platforms should make audit reports available to customers, though some details may be redacted. Absence of certifications isn't automatically disqualifying for smaller platforms, but larger services handling thousands of accounts should demonstrate third-party validation.
CertificationWhat It AuditsRenewal PeriodSOC 2 Type IISecurity controls over timeAnnualGDPR ComplianceEU data protection standardsOngoingISO 27001Information security management3 years (annual surveillance)PCI DSSPayment card data handlingAnnual
For platforms without formal certifications, evaluate their security documentation—do they publish detailed privacy policies, security whitepapers, or incident response procedures? Transparency about security practices matters as much as formal compliance. Learn more about platform evaluation in our platform comparison guide.
Frequently Asked Questions
1. Can automation platforms see my trading strategies?
It depends on the platform's architecture. Server-side platforms that store your full strategy logic can technically access it, though reputable providers have policies against doing so. Platforms that only process TradingView webhook payloads see individual trade signals but not your complete strategy or indicators.
2. What happens to my data if a platform shuts down?
This varies by provider and is rarely detailed in terms of service. Best practice: maintain local backups of your strategy rules and export trade history regularly. Some platforms commit to data deletion within 30-90 days of closure, while others may retain data indefinitely for legal compliance.
3. Are cloud-based platforms less secure than self-hosted solutions?
Not necessarily—major cloud providers like AWS often have stronger security infrastructure than individual traders can implement. The question is whether the platform provider properly configures cloud security, encrypts data, and manages access controls. Self-hosted solutions give you full control but require security expertise.
4. How do I verify a platform's encryption claims?
Check for HTTPS in the URL (verifies TLS in transit). Ask support for technical documentation on encryption at rest. Review security audits or certifications if available. For API connections, test whether credentials are ever displayed in plaintext in the UI or transmitted via unencrypted channels.
5. Should I use different API keys for automation than manual trading?
Yes, if your broker allows multiple API keys with different permission levels. Create a dedicated key for automation with only necessary permissions (typically read + trade execution, not withdrawal). This limits exposure if the automation platform is compromised—the attacker can't withdraw funds or modify account settings.
Conclusion
Data privacy in automation platforms hinges on encryption standards (TLS 1.3, AES-256), storage architecture (server-side vs. client-side), third-party sharing policies, and compliance certifications like SOC 2 Type II. Evaluate what data platforms collect, how they protect it, where they store it, and who else has access. Prioritize platforms with transparent security documentation and verified compliance over those making vague security claims.
Before connecting live accounts, review privacy policies, test with paper trading, and verify encryption implementation. For prop firm accounts, ensure platform practices align with firm data policies. The goal is matching your privacy requirements with platform capabilities—higher-volume traders and those with proprietary strategies need stronger protections than those automating basic rules.
Want to explore platform features beyond privacy? Read our complete platform comparison guide covering execution speed, broker integration, and feature analysis.
References
- AICPA. "SOC 2 Compliance: What It Is and Why It Matters." https://www.aicpa.org/interestareas/frc/assuranceadvisoryservices/sorhome.html
- European Commission. "General Data Protection Regulation (GDPR)." https://gdpr.eu/
- National Institute of Standards and Technology. "Advanced Encryption Standard (AES)." https://www.nist.gov/publications/advanced-encryption-standard-aes
- CFTC. "Customer Privacy and Data Security." https://www.cftc.gov/ConsumerProtection/PrivacySecurity/index.htm
Disclaimer: This article is for educational purposes only. It is not trading advice. ClearEdge Trading executes trades based on your rules—it does not provide signals or recommendations.
Risk Warning: Futures trading involves substantial risk. You could lose more than your initial investment. Past performance does not guarantee future results. Only trade with capital you can afford to lose.
CFTC RULE 4.41: Hypothetical results have limitations and do not represent actual trading.
By: ClearEdge Trading Team | About
Steal the PlaybooksOther TradersDon’t Share
Every week, we break down real strategies from traders with 100+ years of combined experience, so you can skip the line and trade without emotion.