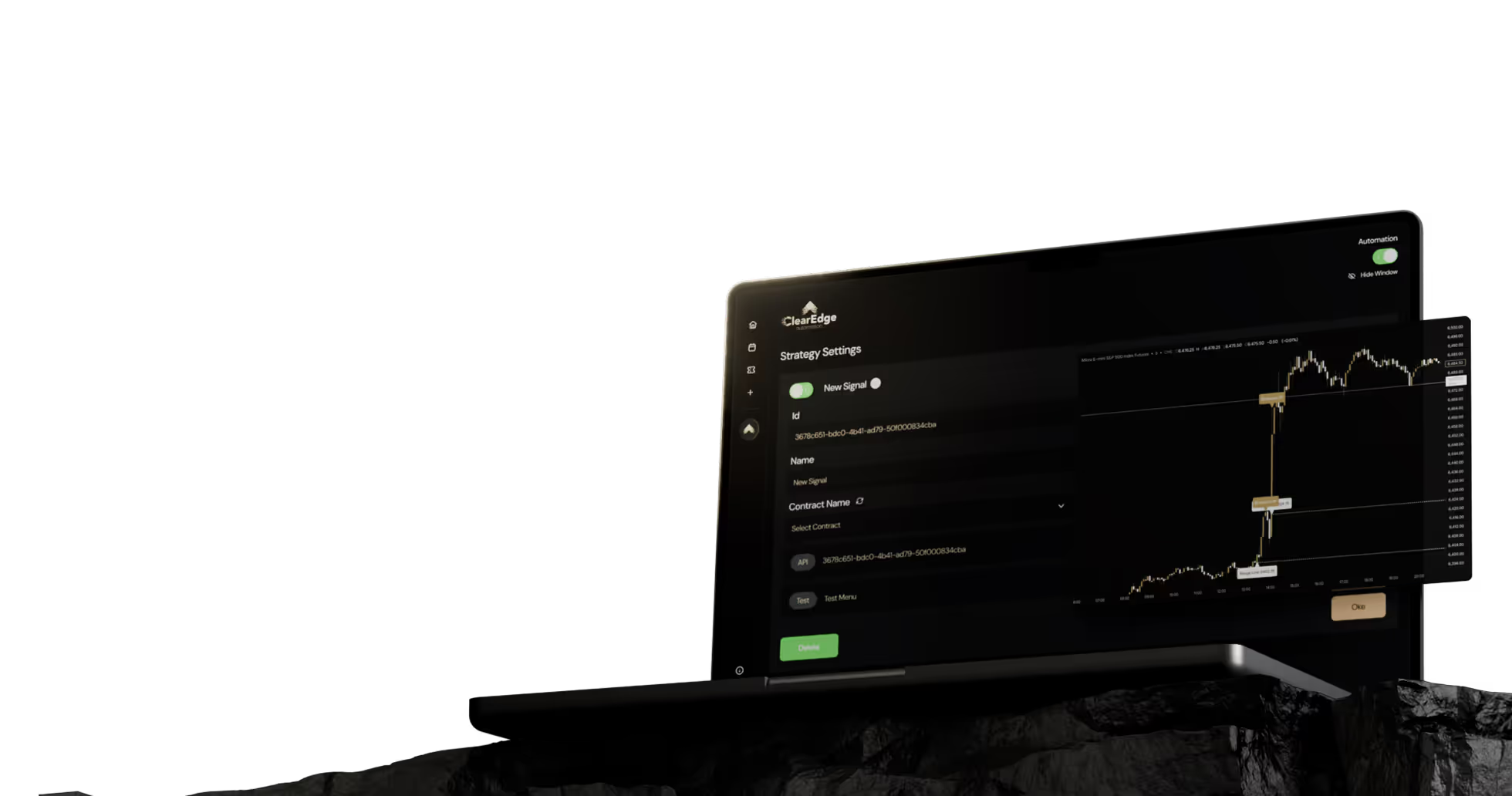
Futures Automation Platform Security Features Checklist For Traders
Secure your futures trading account with our essential security checklist. Evaluate API encryption, 2FA, and webhook validation to keep your strategies safe.


An automation platform security features checklist helps futures traders evaluate whether a trading platform adequately protects their accounts, strategies, and data. Key security factors include API key encryption, two-factor authentication, webhook validation, broker connection protocols, data storage practices, audit logging, and real-time breach detection. Traders should verify each security layer before connecting live accounts to any automation platform.
Key Takeaways
- API key encryption and secure credential storage prevent unauthorized access to your broker accounts
- Webhook validation with secret tokens stops malicious actors from sending fake trading signals
- Two-factor authentication adds a critical second layer of protection beyond passwords
- Audit logs let you track every trade execution and platform access event for security review
Table of Contents
- Why Security Matters in Futures Automation
- Authentication and Access Control
- API Credential Protection
- Webhook and Signal Validation
- Data Encryption and Storage
- Audit Logging and Monitoring
- Broker Connection Security
- Testing and Verification Steps
- Frequently Asked Questions
- Conclusion
Why Security Matters in Futures Automation
Automation platforms connect directly to your broker account and execute real trades with real money. A security breach can result in unauthorized trades, drained accounts, or stolen trading strategies. According to the CFTC, retail futures traders lose an estimated $75 million annually to various forms of fraud and unauthorized access.
When you automate futures trading, you grant the platform permission to place orders on your behalf. This requires sharing API credentials that control your account. Without proper security measures, these credentials can be intercepted, stolen, or misused.
API Key: An API key is a unique identifier that allows an application to access your broker account programmatically. It functions like a password but is designed for software-to-software communication rather than human login.
Security failures in automation can happen at multiple points: during credential transmission, while stored on the platform's servers, during webhook communication from TradingView, or through compromised user accounts. Each vulnerability point needs specific protections.
What Authentication Methods Should Your Platform Use?
Two-factor authentication (2FA) should be mandatory, not optional, for any platform handling live trading. 2FA requires both your password and a time-sensitive code from your phone or authenticator app. This prevents account access even if someone steals your password.
Look for platforms that support authenticator apps like Google Authenticator or Authy rather than SMS-based codes. SMS can be intercepted through SIM-swapping attacks. According to a 2024 study by the National Cybersecurity Alliance, accounts with 2FA are 99.9% less likely to be compromised than password-only accounts.
Session management matters too. The platform should automatically log you out after a period of inactivity and require re-authentication for sensitive actions like changing API keys or withdrawal settings. Check if the platform lets you view active sessions and remotely log out from devices you don't recognize.
How Should Platforms Store Your API Credentials?
Your broker API keys must be encrypted both in transit and at rest. In transit means encryption during transmission from your browser to the platform's servers using TLS 1.2 or higher. At rest means the keys are encrypted in the database, not stored as plain text.
Ask potential platforms directly: "Are API keys encrypted at rest?" If they can't give a clear yes, that's a red flag. Proper encryption means that even if someone gains database access, they can't read your actual credentials without the encryption keys.
Encryption at Rest: Encryption at rest protects stored data by converting it into unreadable code that requires a specific decryption key to access. This prevents data theft even if someone breaches the storage system.
Some platforms implement additional measures like separating encryption keys from the encrypted data, storing them on different servers or using hardware security modules (HSMs). While not always necessary for retail traders, these practices indicate a security-first architecture.
The platform should never display your full API secret after initial entry. Most secure implementations show only the last few characters, requiring you to regenerate credentials if you need to view them again.
How Do You Validate TradingView Webhooks Securely?
Webhook security prevents unauthorized trading signals from executing on your account. Without validation, anyone who discovers your webhook URL could send fake signals and trigger unwanted trades.
The most effective protection is webhook secret tokens—unique strings that TradingView includes in the webhook payload. The automation platform verifies this secret before executing any trade. If the secret doesn't match, the signal is rejected.
When setting up TradingView automation, generate a complex secret token (at least 16 characters with mixed case, numbers, and symbols). Store this in both your TradingView alert and your automation platform configuration. Rotate the secret periodically, especially if you've shared code or screenshots that might expose it.
Webhook Security Checklist
- ☐ Use unique webhook URLs for each strategy or account
- ☐ Implement secret token validation on every webhook
- ☐ Use HTTPS for all webhook endpoints (never HTTP)
- ☐ Monitor webhook logs for unusual activity or failed attempts
- ☐ Rotate webhook secrets every 90 days
- ☐ Never share webhook URLs or secrets in public forums
Some platforms add IP whitelisting, which only accepts webhooks from known TradingView server IP addresses. This adds another validation layer but requires maintenance as TradingView occasionally updates their server infrastructure.
What Data Encryption Standards Matter?
All communication between your browser and the automation platform should use HTTPS with TLS 1.2 or higher. You can verify this by checking for the padlock icon in your browser's address bar and examining the certificate details.
Beyond basic HTTPS, review the platform's privacy policy to understand what data they collect and how long they retain it. Trading data, including your strategies and performance metrics, represents valuable intellectual property. The policy should specify whether this data is encrypted, where it's stored geographically, and who has access.
For platforms storing data in the cloud, ask about their cloud provider's security certifications. SOC 2 Type II compliance indicates the provider undergoes regular third-party security audits. While not a guarantee, it shows commitment to industry-standard practices.
Consider whether the platform stores your trading strategy details. Some platforms only store execution instructions (buy/sell, quantity, price), while others cache your full TradingView indicator logic. Less stored data means less exposure if a breach occurs.
Why Are Audit Logs Critical for Security?
Audit logs record every action on your account: logins, API key changes, webhook executions, trades placed, and setting modifications. These logs let you detect unauthorized access or suspicious activity quickly.
A good automation platform provides detailed logs showing timestamps, IP addresses, and the specific actions taken. You should be able to filter logs by date range, action type, and outcome (success vs. failure). Failed login attempts are particularly important—multiple failures from unknown IPs may indicate an attack attempt.
Check whether the platform offers alerts for specific security events. Email or SMS notifications for login from a new device, API key changes, or unusually large trades help you respond to problems in real time rather than discovering them days later.
Log TypeWhat to MonitorRed FlagsLogin ActivityTime, location, deviceMultiple failed attempts, unfamiliar locationsTrade ExecutionTimestamp, instrument, sizeTrades outside your strategy parametersAPI ChangesWhat changed, when, from whereChanges you didn't makeWebhook CallsSource, validation statusFailed validations, unusual frequency
Log retention periods matter for forensic analysis if something goes wrong. Platforms should retain logs for at least 90 days, with options to export them for your own records.
How Should Platforms Connect to Your Broker?
The connection between the automation platform and your broker should use the broker's official API, not screen scraping or other unauthorized methods. Official APIs have built-in security features and are less prone to breaking when brokers update their systems.
Review which brokers the platform supports and verify they're legitimate FCMs registered with the CFTC. You can check registration status through the NFA's BASIC search system. Unregistered or offshore brokers carry additional risks beyond just automation security.
FCM (Futures Commission Merchant): An FCM is a firm registered with the CFTC that accepts orders to buy or sell futures contracts and accepts money to support those orders. Working with registered FCMs provides regulatory protection for your funds.
The platform should connect using read-write API permissions only for order placement, not withdrawal permissions. Most brokers let you generate API keys with limited permissions—never give the automation platform the ability to withdraw funds from your account.
Some brokers offer IP whitelisting for API access, meaning your API key only works from approved IP addresses. If the automation platform uses dedicated servers with static IPs, this adds valuable protection. Ask if they provide their server IPs for whitelisting.
How to Test Platform Security Before Going Live
Start with simulated trading or paper trading accounts to test the platform's security features without risking real money. Most brokers offer demo accounts with API access that function identically to live accounts for testing purposes.
Try to trigger security features intentionally. Enter the wrong password multiple times to see if you're temporarily locked out. Check if you receive notifications when logging in from a new device. Attempt to modify webhook settings and verify you're prompted for additional authentication.
Review the platform's documentation for security best practices. Well-managed platforms provide specific guidance on securing your account, generating strong secrets, and what to do if you suspect a breach.
Pre-Launch Security Testing
- ☐ Test 2FA setup and recovery process
- ☐ Verify webhook validation blocks requests without proper secrets
- ☐ Check that audit logs accurately record your test activities
- ☐ Confirm API keys aren't displayed in full after initial setup
- ☐ Test session timeout and automatic logout
- ☐ Attempt login from different devices and check notification system
Before connecting live accounts, research the platform's history. Search for any reported security incidents, how they were handled, and whether users were compensated for losses. A platform's response to past security issues reveals their commitment to user protection.
Frequently Asked Questions
1. What happens if my automation platform gets hacked?
If a platform breach occurs, immediately revoke API keys through your broker's website and change all passwords. Contact the platform's support team and your broker to report suspicious activity. Most registered brokers have fraud protection policies, but coverage varies by situation and broker.
2. Should I use the same password for my broker and automation platform?
Never use the same password across different services. If one gets compromised, attackers will try that password on related accounts. Use a password manager to generate and store unique, complex passwords for each service you use.
3. How often should I rotate my API keys and webhook secrets?
Rotate API keys and webhook secrets every 90 days as a baseline security practice. Rotate immediately if you suspect any exposure—shared a screenshot showing keys, had a device stolen, or noticed unusual account activity.
4. Can I limit my API key to only work during specific hours?
This depends on your broker's API capabilities. Some brokers let you set time-based restrictions on API keys, while others don't offer this feature. Check your specific broker's API documentation or contact their support team.
5. What's the difference between API keys and OAuth for broker connections?
OAuth lets you grant limited access without sharing your actual credentials, and you can revoke access anytime from your broker's website. API keys function like passwords with specific permissions. OAuth is generally more secure but not all futures brokers support it yet.
Conclusion
Security should be your first consideration when evaluating any futures automation platform. Verify that authentication, encryption, webhook validation, and audit logging meet industry standards before connecting live accounts.
Use the checklist approach to evaluate each security layer systematically. Test features in demo mode first, and only move to live trading once you've confirmed the platform protects your credentials, validates signals properly, and logs all activity transparently.
Want to compare security features across platforms? Read our complete platform comparison guide for detailed feature breakdowns and setup recommendations.
References
- CFTC. "Customer Advisory: Protect Your Funds." https://www.cftc.gov/LearnAndProtect/AdvisoriesAndArticles/ProtectYourFunds.html
- National Cybersecurity Alliance. "Multi-Factor Authentication Statistics 2024." https://staysafeonline.org/resources/multi-factor-authentication/
- NFA. "BASIC Search System - Verify Registration." https://www.nfa.futures.org/BasicNet/
- TradingView. "Webhooks and Alerts Documentation." https://www.tradingview.com/support/solutions/43000529348-about-webhooks/
Disclaimer: This article is for educational and informational purposes only. It does not constitute trading advice, investment advice, or any recommendation to buy or sell futures contracts. ClearEdge Trading is a software platform that executes trades based on your predefined rules—it does not provide trading signals, strategies, or personalized recommendations.
Risk Warning: Futures trading involves substantial risk of loss and is not suitable for all investors. You could lose more than your initial investment. Past performance of any trading system, methodology, or strategy is not indicative of future results. Before trading futures, you should carefully consider your financial situation and risk tolerance. Only trade with capital you can afford to lose.
CFTC RULE 4.41: HYPOTHETICAL OR SIMULATED PERFORMANCE RESULTS HAVE CERTAIN LIMITATIONS. UNLIKE AN ACTUAL PERFORMANCE RECORD, SIMULATED RESULTS DO NOT REPRESENT ACTUAL TRADING. ALSO, SINCE THE TRADES HAVE NOT BEEN EXECUTED, THE RESULTS MAY HAVE UNDER-OR-OVER COMPENSATED FOR THE IMPACT, IF ANY, OF CERTAIN MARKET FACTORS, SUCH AS LACK OF LIQUIDITY.
By: ClearEdge Trading Team | 29+ Years CME Floor Trading Experience | About
Steal the PlaybooksOther TradersDon’t Share
Every week, we break down real strategies from traders with 100+ years of combined experience, so you can skip the line and trade without emotion.